Click-level fraud is where fraud becomes costly, as the impression leading to the click has been purchased and so platforms and advertisers are paying for the fraudulent traffic in time and money. We talked about the importance of location, timing, events, and site-level considerations when catching fraud at the impression-level, now we’ll talk about some of the methods used to defraud at the click: click spam / click flooding, click injection, and click hijacking. We’ll also dive in to how the type of targeted device, whether Android or iOS, can affect your campaign’s vulnerability.
Click Spam
Click spam is possibly the mother of all adfraud types. Much of the fraudulent activity we will discuss in this article is a development of click spam to a degree. So how does click spam work? At the most basic levels it can described as the act of a fraudster executing a click for a user who has not clicked an ad, or as the act of claiming credit for a click not driven by the fraudster. For app developers, this can be done to artificially improve the performance of their adspace and thus increase the $CPM value of their traffic, whereas for malicious networks, it can be done to steal credit for clicks and installs driven by legitimate networks, artificially improving the performance of their campaigns. Some of the ways click spam is executed include the following:
- A fraudulent app can execute clicks for ads while in standby or ‘minimized’. These ads are requested, populated and executed after being cached during the user’s engagement with the app
- A fraudster could use malicious code to run clicks in the background while a user interacts with an app, making it look like the user is clicking on any ads served during that time.
- A fraudster could intercept the impression and send impressions-as-clicks, making views look like engagements.
If a significant volume of these clicks are sent out in a short space of time, it is known as click flooding. A side-effect of this kind of click fraud is that, as organic installs can be misattributed to fraudsters if they “inject” the spoofed click at the right time, organic install and organic lift studies can become skewed and lose relevance. This brings us to our next topic…

Click Injection
Click injection is a sophisticated version of click spam where an installed app or advertisement SDK allows the fraudsters to listen to broadcasted signals from devices which indicate that users are downloading apps. Then, moments before installs occur, the fraudulent app or advertisement SDK will send a click, claiming credit.
While click injection is typically more common on Android due to iOS’ “sandboxing” – the isolating of applications from critical system features (such as the broadcasts about app installs just mentioned) – there have been recent cases of click injection uncovered on iOS due to malicious advertisement SDKs that were not caught by the App Store’s screening.

iOS 14 will further sandbox iOS devices by taking device-level user information away from apps that lack permission, making click injection types of ad fraud more difficult, but that doesn’t mean fraudsters will quit. In fact, they will most likely develop even more sophisticated means of deception to steal ad dollars and we’ve already noticed (and blocked) new forms of iOS click spam attempting to infiltrate our campaigns. These will be discussed in a later blog post.
Click Hijacking
This is simply another way to say click injection, but specifically injection that is piggybacking on an install from the legitimate clicking of an ad by a user. A real click is occurring somewhere in the process, the malicious app or SDK intercepts that click signal and sends a click of their own attempting to trick the MMP into attributing the install to the fraudster due to ‘last click’ attribution.
What to Watch Out For
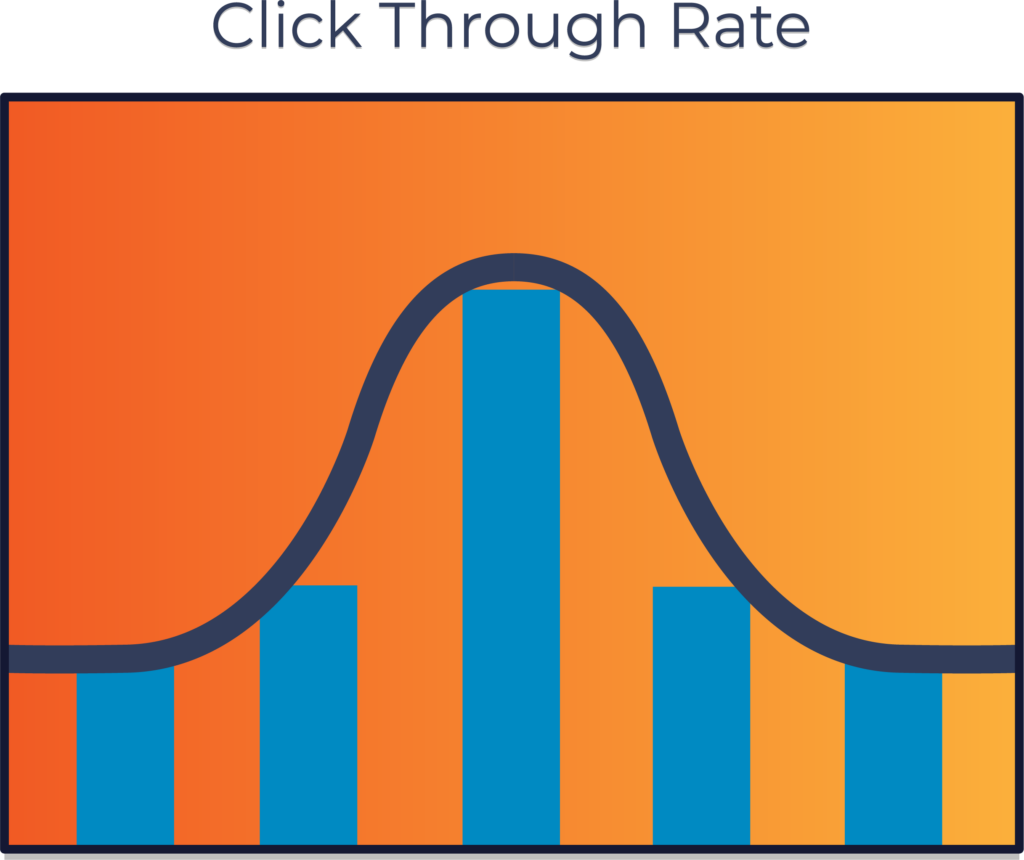
As discussed in previous blog posts, it’s important to pay attention to the timing of clicks. When did the click occur? If you have a click and no impression, that’s fraud. It’s also important to consider the CTRs when looking for click-level fraud. There is such a thing as “too good” a CTR. Compare the sources you’re seeing in your reporting: if one app has a much higher CTR than others, it may be too good to be true.
Consider too the payment practices of your mobile advertising partners and be mindful of sites and platforms that operate on a CPC basis because click-level fraud is most likely to occur there, where the value lies in the click.
Be vigilant as you review your reports – look for anomalies at device-level and site-level, for impressions, clicks, and conversions. Make sure the numbers make sense, and if you aren’t sure, investigate. Fraudsters are getting more sophisticated as technology develops, but if advertisers and their mobile partners work together, we can catch them out easily.
 Português
Português 韓國
韓國 日本
日本